Overview
The multibillion-dollar gaming company has had professional exponential increase within the last few years, drawing throngs of game enthusiasts from all around the world. As digital ecosystems get larger, cybersecurity in gaming is turning into increasingly more essential. Cyberattacks within the sports activities enterprise ought to have critical results, along with monetary loss, compromised personal facts, and reputational damage. Robust cybersecurity measures preserve the authenticity of the gaming enjoyment by safeguarding individual gamers and gaming communities.
The Evolution of Cyber Threats in Online Gaming
Early Cyber threats to gaming were noticeably simple to pick out and typically worried simple hacks and approaches intended to give gamers an unfair benefit over other players. However, as the field grew and the dangers extended, Cyber threats likewise became greater elaborate and complicated. These days, scammers use advanced techniques like ransomware, phishing, and disbursed denial-of-provider (DDoS) attacks to goal each man or woman gamers and gaming agencies. In order to combat the dangers of today, one needs to have surprisingly sophisticated defenses and hold regular vigilance.
Moreover, the rise of augmented truth (AR) and digital truth (VR) offers special protection demanding situations because of the truth that the ones doing immersive research reap and manage touchy personal records approximately people. The collection and alertness of biometric information in VR/AR gaming memories has also introduced private concerns. More ability assault vectors also are created by means of the growing integration of Internet of Things (IoT) devices into gaming environments, in view that the ones networked gadgets could not have robust security measures.
In order to fight the constantly converting threats, recreation creators and platform agencies want to prioritize turning in cybersecurity talents including encryption, multi-thing authentication, regular safety audits, and consumer training. Cooperation between law enforcement agencies, cybersecurity experts, and enterprise stakeholders is essential to stopping cyber attacks and retaining the security and integrity of the gaming community.
Common Cyber Threats within the Gaming Sector
Typical dangers that gamers face whilst playing on line are:
Phishing assaults
Approach of operation;
Cybercriminals use phishing emails, messages, or pop-usa that appear to be from elite gaming corporations. These messages often lead customers to click on doubtful hyperlinks or view personal data including usernames, passwords, or pricing info.
– Impact: Following the purchase of the statistics, hackers may additionally benefit from access to personal information, debts from gambling, and business charges. This would possibly lead to identity theft and financial loss.
An example of this could be: Users acquire a phishing email that appears to be from a well-known gaming platform, soliciting for them to confirm their account with the aid of clicking on a hyperlink that ends in a phony internet site intended to steal their login credentials.
Takeover of Accounts
How it unquestionably features;
Hackers exploit credentials they have stolen or wager to gain admission to the gaming cash owing. They can employ phishing, brute force assaults, or credential stuffing—which entails the use of previously received facts—to attain these credentials.
– Impact: Compromised money owed may be used for unauthorized purchases, income from unusual objects, and in-activity foreign exchange. Financial statistics that are linked to personal statistics are likely to be misused.
An example might be if a hacker gained legitimate access to a player’s account after which sold the participant’s priceless in-activity topics on the darknet.
Malicious software
Malicious software programs may be found in hacks, interest tweaks, and enhancements that appear genuine. This is how viruses and malware work. Gamers’ PCs grow to be inflamed with malware, which can be downloaded and mounted to scouse, borrow facts, record keystrokes, or cause different harm.
– Impact: Malware may be the reason for monetary robbery, compromised private records, and misplaced data. It may also result in reduced machine performance.
– For instance, while a player downloads a cheat tool for a famous game, it secretly installs a keylogger that data every keystroke they make, consisting of passwords and credit card data.
Distributed Denial of Service (DDoS) assaults
How it genuinely functions:
Attackers can overload gaming servers with excessive bandwidth the use of a community of compromised gadgets, resulting in disruptions or entire outages.
– Impact: Players experience lag, disconnections, and issues getting access to undertaking gives. As a result of the give-up, game enthusiasts may also end up angry, and gaming corporations may additionally incur losses.
–Example: Due to a centered attack on the servers of a popular online game, hundreds of players are disconnected and unable to participate on an excessive occasion.
Ransomware
Ransomware is a sort of malicious software that encrypts a sufferer’s files and needs a ransom to release them. This is how it works. Phishing emails, malware downloads, and software bugs are some of the ways it may unfold.
Effect: Sufferers choice to pay a ransom to gather returned their right to access their documents and retrieve their data. Data recovery isn’t assured to work even in case you pay.
– For example, a gamer may additionally by chance download ransomware, which encrypts all of their personal files and recreational facts and needs bitcoin in exchange for the ability to decrypt the documents.
In-Game Fraud
How In-Game Fraud Clearly Operates: Scammers trick gamers into giving up in-recreation forex or topics via misleading gives, fake gives, or guarantees of particular gadgets or interest enhancements.
– Effect: Gamers face the danger of being the next rip-off victim further to losing priceless in-sport devices.
– Instance: A con artist sends in-challenge foreign exchange to a player in exchange for a super object, however the scammer disappears earlier than the item is delivered.
Data Breach:
How It Happens;
Cybercriminals target gaming companies so that you can take advantage of considerable amounts of customer statistics, including charge information, login credentials, and personal records. These hackers often make the most weaknesses in the businesses’ security strategies.
Impact: The selling of stolen information on the dark internet can also result in identification robbery, economic fraud, and extra attacks on patients.
Example: Due to a breach inside the database of a major gaming organization, tens of millions of purchasers’ e-mail addresses, passwords, and credit card records are available.
Cheats and Exploits
– How it works: To acquire unfair advantages in video games, players make use of unapproved programs or modifications, called cheats. These programs might also include wallhacks, aimbots, and different exploits.
Impact: These cheats frequently consist of hidden viruses which could infect the user’s gadget further to interfere with other people’s gaming reviews.
Example: In a multiplayer game, a participant utilizes a hack to get an advantage over other players, but the cheat software also installs spyware that tracks the person’s moves.
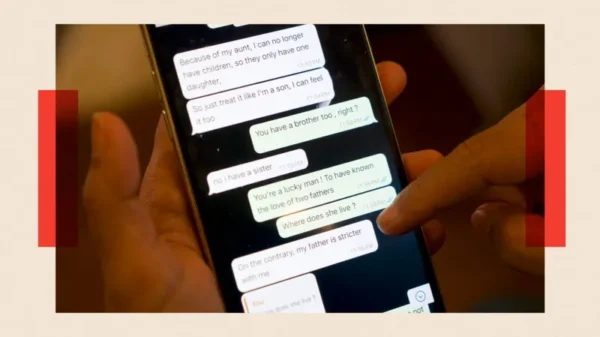
Employing Social Engineering
– How it operates: Through interpersonal interactions, whether in-sport or online, attackers coerce victims into disclosing touchy facts or taking acts that jeopardize protection.
– Impact: Unintentionally disclosing passwords or non-public facts, or maybe giving the attacker cash or in-sport assets, is possible for sufferers.
– Example: Under the pretense of requiring assistance or presenting to proportion resources, an attacker befriends a player in-game and finally persuades them to disclose their account login information.
Unauthorized Exchanges
– How it really works: Through compromised gaming accounts, hackers usually use credit card records that have been stolen to make transactions in video games.
The impact on sufferers is each monetary loss and the problem of combating unjustified prices. Additionally, there will be an upward thrust in chargebacks and a decline in trust for gaming groups.
– Example: A hacker purchases in-sport forex and thinks about the use of credit card credentials that they’ve stolen, leaving the sufferer’s announcement amazed by prices.
Malware
Gamers are at extreme risk from malware, which incorporates ransomware. Updates that seem prison can also comprise malicious malware that users by accident download. While other applications can steal confidential information or intrude with gaming, ransomware encrypts the sufferer’s records and demands a fee to liberate it.
Cyberthreats’ Effect on Participants and Businesses
There are vast ramifications for both game enthusiasts and gaming organizations from cyber threats inside the gaming industry. Players may additionally revel in immediate coins losses because of compromised bills or in-sport purchases, as well as identification robbery risks associated with the loss of personal information. In addition to the economic charges, cyberattacks may have mental repercussions like strain and tension, that could make gaming less enjoyable.
Cyber threats can free gaming corporations lots of cash because they now not handiest reason for direct theft but additionally incur charges for combating attacks, repairing harm, and compensating impacted customers. Furthermore, an organization’s logo may be significantly broken by way of cyberattacks, that could result in a drop in user engagement and a lack of customer agreement. Legal repercussions and elevated regulatory oversight are viable long-term effects.
Protective Steps for Players
Players want to implement robust protection strategies to defend themselves from cyberattacks. The risk of account hijacking may be appreciably reduced through putting in -issue authentication (2FA) and the usage of robust, one-of-a-kind passwords for gaming debts. In addition, users should exercise caution while downloading documents and surfing the internet, making sure to deal most effectively with dependable web sites and spotting phishing scams. Updating operating systems and security software on an everyday foundation improves protection towards the maximum latest threats, and preserving an eye out for new weaknesses and studying the way to save them strengthens security usually.
Steps to Preserve the Rights of Gaming Companies
Gaming companies need to make use of modern safety features to protect personal facts and their structures. Sensitive statistics should constantly be encrypted to prevent unauthorized parties from reading it, even in the event that it is intercepted. Regular vulnerability assessments and safety audits are useful resources in finding gadget vulnerabilities and addressing them before they are used in opposition to the machine.
Programs for worker focus and schooling are critical for thwarting social engineering scams. Businesses can lower the hazard of inner security breaches by way of teaching employees approximately the maximum current cyberthreats and safe tactics. Furthermore, having properly-defined incident response procedures guarantees a green and short reaction to any protection occurrences, reducing harm and recovery time.
Technology’s Contribution to Strengthening Cybersecurity
Innovations in this era are important to enhancing game cybersecurity. Real-time danger detection and response may be completed by means of using artificial intelligence (AI) and device studying. By examining developments and abnormalities in community records, these technologies can spot possible cyberattacks earlier than they have a threat to do quite a lot of damage.
An additional diploma of protection is furnished via blockchain technology, especially on the subject of transaction safety and data integrity. Through the use of cryptographic algorithms and decentralized records storage, blockchain lowers the possibility of information manipulation and unauthorized entry to.
Gaming structures are covered by way of scalable and adaptable cloud security answers. Gaming businesses can take advantage of current protection features like allotted denial-of-service (DDoS) protection, automatic updates, and sturdy access regulations via using cloud offerings as opposed to a large on-premises infrastructure.
Cybersecurity Regulations and Compliance in Gaming
International cybersecurity laws have a significant impact on how gaming companies handle security. Adherence to global norms such as the California Consumer Privacy Act (CCPA) in the US and the General Data Protection Regulation (GDPR) in Europe guarantees that businesses implement strong security and transparency protocols.
For gambling enterprises, however, compliance can be difficult, particularly if they operate in numerous jurisdictions. It takes a thorough grasp of the law and the application of uniform security procedures in every area of operation to successfully navigate the intricate web of rules. Governments and regulatory agencies are essential in upholding these standards and assisting businesses with their compliance initiatives.
Case Studies: Notable Gaming Cyberattacks
Analyzing prominent cyberattacks in the gaming sector offers important insights into the strategies used by cybercriminals and the weaknesses they take advantage of. Strong security protocols and prompt breach response were underlined by the 2011 Sony PlayStation Network hack, which exposed the private data of over 77 million accounts.
Ransomware was used in the 2020 cyberattack against CD Projekt Red, the company that creates well-known video games including Cyberpunk 2077 and The Witcher series. The attack resulted in the loss of crucial data and source code. The necessity of ongoing security monitoring and quick incident response was highlighted by this occurrence.
Additional noteworthy hacks, including the assaults on Ubisoft and Electronic Arts (EA), highlight the continual dangers that the gaming sector faces and the vital significance of cybersecurity awareness.
Prospects for Gaming Cybersecurity Trends
Cybersecurity in the gaming industry will be influenced by new developments and changing threats. Cyber risk prediction and mitigation will be greatly aided by predictive analytics and threat intelligence. These systems can enable proactive protection measures and offer early warnings of potential dangers by analyzing large volumes of data and spotting trends.
The advent of blockchain-powered decentralized gaming systems is expected to improve security by removing potential points of failure and lowering the likelihood of data breaches. Furthermore, recent developments in biometric security, such facial and fingerprint recognition, provide fresh approaches to user authentication and account protection against unwanted access.
Answers to Common Questions (FAQ)
Which cyberthreats affect gaming the most frequently?
In the gaming industry, common cyberthreats include ransomware and malware, phishing schemes, DDoS assaults, and social engineering techniques.
How can gamers defend themselves against online dangers?
By creating strong passwords, turning on two-factor authentication, being wary of phishing efforts, and routinely updating their operating systems and security software, players can keep themselves safe.
What steps should the gaming industry take to improve cybersecurity?
Gaming businesses should put in place cutting-edge security procedures, carry out frequent security audits, teach staff members cybersecurity best practices, and create explicit incident response plans.
What part does AI play in cybersecurity for gaming?
By examining patterns of network traffic and spotting anomalies that can point to cyberattacks, artificial intelligence (AI) and machine learning are able to recognize and react to threats instantly.
What effects do international laws have on cybersecurity in gaming?
International laws, including
Higher standards of cybersecurity are ensured by GDPR and CCPA, which force gaming firms to use strong security measures and uphold transparency in the management of user data.
Key Takeaway
In order to defend against increasingly complex cyberthreats, gaming companies and players alike must prioritize cybersecurity. The gaming sector may reduce risks and guarantee a secure and pleasurable experience for all by implementing strong security protocols, utilizing cutting-edge technologies, and adhering to international rules. Maintaining the integrity and security of the digital gaming industry will require constant innovation and awareness as cyber threats continue to change.