Since its initial release, Apple has addressed a long-standing bug that compromised a privacy feature in its iPhone and iPad software. Apple revealed a new feature in iOS 14 back in 2020 that would stop access points and wireless routers in the area from obtaining the specific MAC address of an Apple device.
There are many reasons to track MAC addresses, such as giving network managers the ability to identify all devices—including unauthorized ones—connected to their systems. On the other hand, MAC addresses may be used to track a device over many networks.
The iOS feature would utilize a distinct “private address” for each network instead of sharing the device’s unique MAC address.
But as security researchers Tommy Mysk and Talal Haj Bakry have found, this feature hasn’t functioned as planned since its first release. They found a bug that stopped the privacy feature from operating as intended.
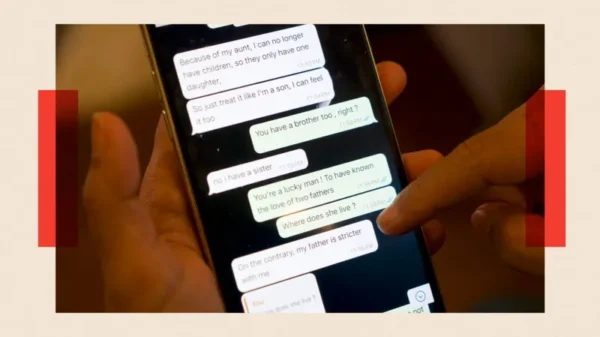
Mysk clarified in a video released this week that although iOS has replaced the device’s actual MAC address with a randomly generated one for every network, the software on the device has also included the virtual MAC address in the queries that an iPhone sends to AirPlay when it connects to a web Then, every other networked device was broadcast to these confirmed MAC addresses.
Even when using a VPN, Mysk said there was no way to stop iPhones and iPads from submitting AirPlay discovery requests. “This is how Apple’s devices find AirPlay-capable devices on the network.”
Mysk attested to TechCrunch that even when users activated Lockdown Mode—an optional feature intended to thwart highly focused cyberattacks—iPhones and iPads continued to submit these requests.
According to Mysk, he initially became aware of this problem in July and, on July 25, sent Apple a security report. Mysk told TechCrunch that getting in touch with Apple was a “huge barrier,” adding that the tech behemoth could not reproduce the “simple” problem until he received word on October 3 that a remedy was ready for testing.
Known as CVE-2023-42846, Apple patched the issue this week and released iOS 17.1 and iOS 16.7.2 for older iOS 16-compatible devices. Devices running iOS 14 or iOS 15 are still susceptible, as Mysk pointed out.
Apple has not published the flaw’s severity; however, according to Mysk, the vulnerability is rated as “high” by the vulnerability ranking system.
Scott Radcliffe, an Apple representative, failed to respond to inquiries from TechCrunch.
With iOS 17.1, Apple addressed several other vulnerabilities, such as one that would have let a hacker get unauthorized access to passkeys and another that might have revealed private information to a hacker with physical access to a device through a Siri fault.