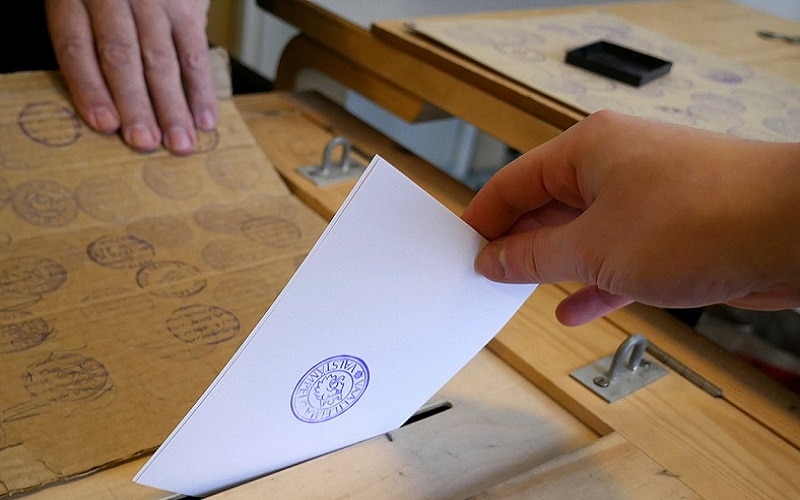
Def Con, one of the world’s largest Hacker’s Conferences, is going down right now – and hackers are hard at work testing the mettle of United States voting security.
They hope to bring potential security flaws to the US government, so the government can further investigate whether or not they may have been used in the US election – and also so the voting system’s flaws can be rectified.
The conference began today, August 10th, and will continue through this weekend, with some dedicated hackers opting to burn the midnight oil in an attempt to further their efforts to crack the system.
Jeanette Manfra, assistant secretary of cybersecurity and communications at the U.S. Department of Homeland Security, shared some thoughts on the Convention and process in an interview with Reuters.
“We see a lot of value in doing things like this,” said Manfra. “The idea is, when we find things here, how do we connect them with the actual vendors and make sure that we are closing this loop back to a coordinated vulnerability disclosure process.”
This event will mark the second iteration of the con’s “Voting Villiage”. The first was created in response to U.S. investigators concluding that the Russians used hacking in an effort to support Donald Trump in the 2016 Presidential Election. Moscow has denied all claims of foul play.
The event has bore significant fruit in the past. In its first year, a Danish hacker discovered a method to take control of a digital touchscreen voting machine that was in use until 2014. According to the hacker, the process of hijacking control could be executed discreetly from up to 1,000 feet away.
This year, the conference has invested in five different types of voting machines that users will have the chance to hack into, some of which are the same models as machines being used in current elections.
So what do the officials have to say about this process. According to the National Association of Secretaries of State, they’re grateful for the efforts being done to strengthen security, but also warn of a potential flaw in their operation.
“It utilizes a pseudo environment which in no way replicates state election systems, networks or physical security,” the Association said in a statement.
This is important to consider when thinking about the viability of these hacks in a realistic voting environment. While being able to take control of a touchscreen machine from 1,000 feet away seems very dangerous when a single voting machine is being surrounded by thousands of hackers, it seems much less plausible when one considers that hijacking control of a touchscreen device means a user can only take control of a single machine at a time. In addition, the voter would still need to input their data before hijacking a touchscreen would be of any use to a hacker, and voters would quickly begin to notice when their taps aren’t matching up with the screen’s display.
In other words, in a realistic setting, methods like this would more likely result in some machines being quickly shut down and investigated rather than changing the course of a presidential election.
Still, this Danish hacker did expose a serious flaw in the machine in question, and by exposing flaw after flaw, these hackers are making the United States’ voting systems safer than they have been in the past.















































Caroline Walker
August 14, 2018 at 1:34 am
Great they are testing this, but sad that they have to
Maya Asregadoo
August 14, 2018 at 2:46 am
It’s good to see hackers garnering positive headlines!